As businesses large and small become more dependent on electronic data, a major focus has shifted towards information security. Businesses are investing more than ever to protect themselves from dozens of security threats, from malware infections to financial fraud.
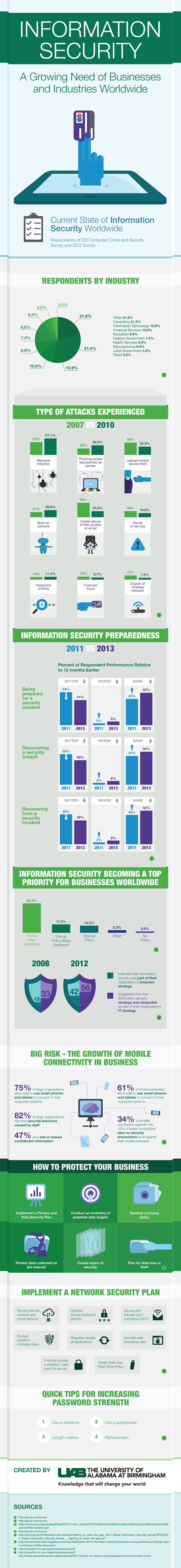
In a survey of businesses worldwide almost every industry surveyed had experienced an information security-based incident at some point in time. In the survey conducted, respondents covered numerous industries with the majority being from the Information Technology side and making up 10.9% of all those surveyed. This is followed by industries such as financial services, education, the Federal Government, health and manufacturing, in that order, among others. 41% of this mix admitted to having faced a security threat. To learn more about our Online Master of Science in Management Information Systems and how it correlates to Electronic data check, out the University of Alabama at Birmingham website.
From 2007 to 2010, the kind of attacks, although the same, have risen in occurrence.
- Malware infections are up to 67.1%
- Phishing is at 38.9%
- Device theft stands at about 33.5%
- Other forms have been bots on the network, insider abuse, denial of service, password sniffing, financial fraud and misuse of wireless networks.
Almost 75% of major organizations today encourage staff to use their personal devices to connect to corporate systems. In small businesses, this stands at 61%. As a result, almost 82% of large companies have reported a breach of security by their own staff.
As information security becomes more of a priority in the future, here are a few things your organization can start doing now to protect itself:
- Implement a privacy and data security plan
- Conduct an inventory of potential data targets
- Develop a privacy policy
- Protect data collected online
- Create levels of security
- Plan ahead for data loss
A Network Security plan is also needed, and of course the ability to create strong passwords is a must to better handle security issues.
To learn more about information security and businesses, take a look below at the infographic created by the University of Alabama at Birmingham.
Add This Infographic to Your Site
